Martin Herfurt
Short Bio
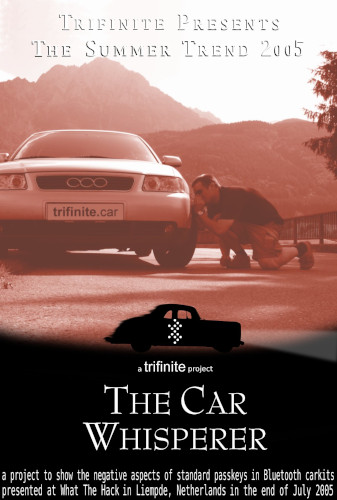
Martin is an independent security researcher focusing - but not exclusively - on various aspects of product security related to Bluetooth wireless technology. As one of the co-founders of the trifinite.group, Martin worked with the Bluetooth SIG, helping the technology and its adopters overcome early design and implementation issues. Martin holds a master’s degree in telecommunications engineering from the University of Applied Sciences in Salzburg. During the last year, he spent his free time to investigate security issues with Tesla vehicles. As part of his fascination with rapid developments in IT technology, Martin has been a regular participant and speaker at the Chaos Communication Congress (CCC) and other international IT security conferences since 1997.