Long Distance Snarf
Aug 2004
3 mins read
The long-distance-snarf is an experiment that took place in the early morning of 4th August 2004 at the Santa Monica Pier in California. Five people (John Hering, James Burgess, Kevin Mahaffey, Mike Outmesguine and Martin Herfurt) made it out of their beds and met a crew of the TV station G4TechTV.

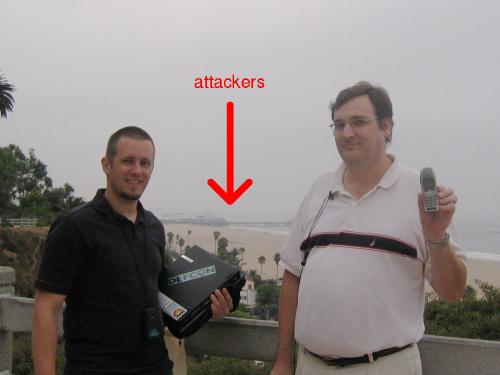
After doing interviews, we finally did the experiment. Therefore, Mike a G4TechTV Crew member with a camera and Martin went up to an elevated place wich was exactly 1.08 miles (1,78 km) away from the Santa Monica Pier. John, James and Kevin stood at parking lot of the Pier and prepared the equipment used for the experiment.
Experiment
In the experiment itself the attacker-team was aiming the antenna at our elevated location. The reason we had to be elevated has to do with the Fresnel Zone that has to be taken into account when dealing with directional radio signals. For ideal results, the radio signal has to fatten out on the way to its destination.
After a little trouble finding the phone device over the high distance, the unbelievable happened. The display of the Nokia phone that Mike held with his outstreched arm showed the typical things that are displayed when a BlueBug attack takes place. First a text saying “Connected to …” appears and then a small headset symbol is displayed. This has been a real eye-opener. Bluetooth Class 2 radios that are used in mobile phones have a typical range of 10 meters. This experiment shows that it is possible to connect to such a class 2 device from about 170 times the range than specified.
What could have been done over this huge distance was a a full BlueBug attack including the reading of the phonebooks and the sending of an SMS.
Of course this world-record setting attack makes it even clearer how much of a risk the BlueBug attack could be to owners of vulnerable phones.
Equipment
The equipment used fot this experiment was the following:
A Dell Laptop running Slackware Linux 9.1 and the Bluez libraries and utilities version 2.9
A modified Linksys Bluetooth USB adaptor with external antenna connector
A high gain (19dbi) panel antenna (most likely of the type Short Backfire)
An unmodified Nokia 6310i phone
Press
Welcome To Long Distance Bluesnarfing - LOOSE wire [en]
Austrian researcher Bluesnarfs at 1.08 miles - engadget [en]
Bluetooth Researchers Keep Breaking Records - theunofficialbluetoothweblog [en]
Three things to scare you - REDHERRING [en]
Wi-Fi Shootout in the Desert - esato [en]
Security Cavities Ail Bluetooth - Wired News [en]
Bluetooth Range Record [en]
… more english citations
Bluetooth-Attacken auf Handys aus fast 2 km Entfernung - golem [de]
Bluetooth-Angriffe auf große Distanz - futurezone [de]
Bluetooth-Angriffe aus großer Entfernung - heise [de]
… more german citations
People Involved
As mentioned above,John Hering, James Burgess, Kevin Mahaffey, Mike Outmesguine and Martin Herfurt were involved in this experiment.
If you have questions concerning the Long-Distance-Snarf experiment, feel free to ask Martin Herfurt.
Sharing is caring!